![HIPAA Compliance [2025]: Components, Privacy Rules, and PHI](https://cybersecurity24x7.com/wp-content/uploads/2025/08/HIPAA-Compliance.png)
The issue of data privacy in healthcare has gained momentum soon after digitalization became a buzzword. With the increasing scale and complexity of data breaches, preserving patient’s privacy came at the forefront.
The impact of such incidents were not just limited to patients, healthcare businesses too faced the brunt as the average cost of breach increased exponentially.
That’s where HIPAA comes in. This is a federal law and it was signed by President Bill Clinton on Aug. 21, 1996. In layman’s jargon, it’s a set of rules aimed to address data privacy and security concerns of all related stakeholders in the medical field.
In the blog, we’ll discuss in detail about the HIPAA laws, why it matters, different components, and how to implement it.
HIPAA stands for “Health Insurance Portability and Accountability Act. Its purpose is to let people change jobs without losing health coverage, standardize how medical bills get processed, and protect sensitive patient data from misuse.
Now the question is who oversees it and who enforces the rules.Healthcare got digital fast. But patient privacy didn’t keep up. As hospitals moved records online, attackers moved in.
Breaches exposed everything from diagnosis to billing details—and not just once. The cost of each breach hit both patients and providers hard, with losses climbing into the millions.
HIPAA was created to stop that spiral. Signed into law by President Bill Clinton in 1996, it set the first national rules for how medical data should be handled, shared, and protected.
At its core, HIPAA does three things:
Two separate agencies run the show:
The OCR’s approach evolved over the past couple of decades. It is just no more limited to responding to complaints and conducting surprise audits. In 2019, OCR collected $28.7 million in settlements. By 2023, that number witnessed a surge to $89.4 million. The message is clear: compliance failures cost real money.
Protected Health Information (PHI) refers to all data that determines a person’s identity. HIPAA lists 18 identifiers that make health information “protected”:
Who Has to Follow HIPAA Rules
A business associate refers to any person or an entity that performs specific actions on behalf of a covered organization. It includes the following:
Components of HIPAA
HIPAA laws has 5 main components:
Title I: Health Insurance Protection: prevents people from losing health coverage when they change or lose jobs.
Title II is mostly related to healthcare organizations as it contains the Privacy Rule, Security Rule, and Breach Notification requirements.
HIPAA Privacy Rules
A main goal of the HIPAA Privacy Rule is to make sure that individuals’ health information is duly protected and ensure quality healthcare. It safeguards personal health information by placing conditions and limits on the disclosure and use of PHI, without patient permission.
It clearly specifies rules to prevent access to PHI, patient rights to obtain PHI, the content of notices of privacy practices, and the use and disclosure forms. The Privacy Rule created America’s first nationwide framework for protecting patient health information. Before HIPAA, no federal law governed how hospitals, doctors, or insurance companies handled medical records.
The Privacy Rule covers PHI in every format that includes electronic, paper, and spoken. It sets limits on who can access patient data and when.Minimum necessary standard is only access to the PHI you need for your job.
A billing clerk doesn’t need to see psychiatric notes. A nurse doesn’t need full medical histories to schedule appointments.
Patient Rights Include:
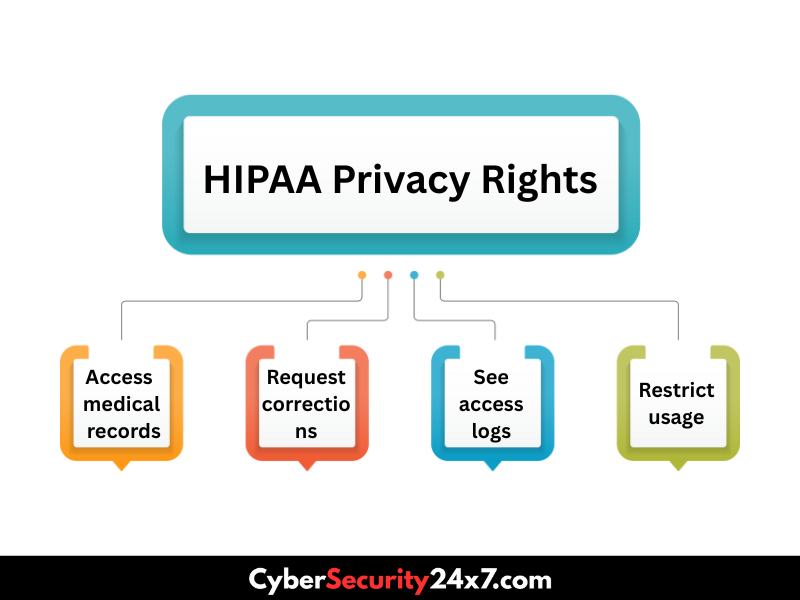
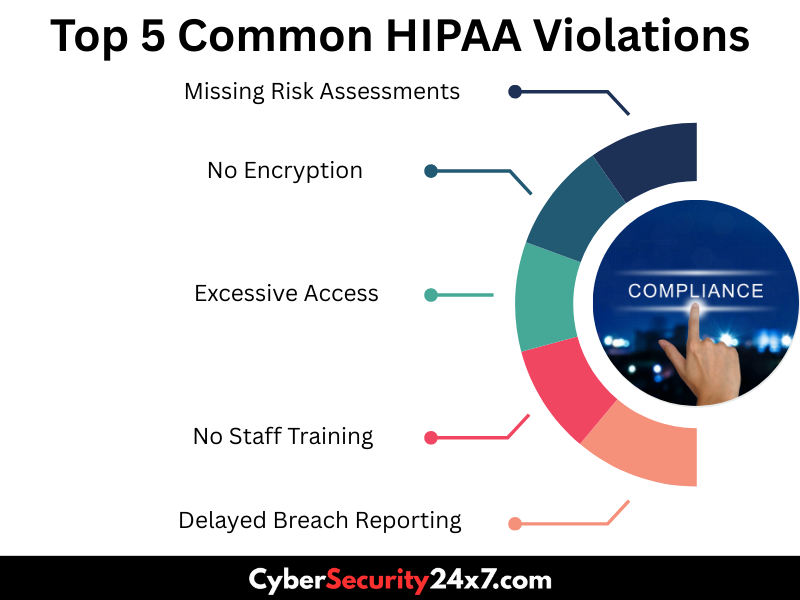
Most violations happen when staff access records they don’t need. Want to know in detail? Click here: HIPAA Privacy Rule
HIPAA Security Rule: Protecting Electronic Health Records
The Security Rule focuses on electronic PHI (ePHI). Every covered entity must protect ePHI’s confidentiality, integrity, and availability through three types of safeguards:
Administrative safeguards include the following:
Physical safeguards include the following:
Technical safeguards include the following:

Notification Timelines:
The Change Healthcare breach in 2024 cost millions and exposed 190 million records due to hacking. The Yale New Haven Health System breach in 2025 affected over 5.5 million individuals, also due to hacking. These high-profile incidents highlight the critical importance of timely breach response and notification.
Compliance isn’t about checking boxes. It’s about creating systems that protect patient data automatically.
It has 7 core elements:
Risk Assessment Requirements:
Most organizations fail at risk assessment. They assume their EMR vendor handles security, but HIPAA makes the covered entity responsible for protecting PHI regardless of where it’s stored.
Some of the popular examples of consequences are:
Criminal penalties apply when violations involve intent to sell PHI or cause harm. Maximum sentences include 10 years in prison and $250,000 in fines.
HIPAA compliance starts with understanding your data. You should map where PHI lives, how it moves, and who touches it.
Practical steps include :
It is essential to understand that technology alone won’t ensure compliance. The biggest risks come from human error, such as employees emailing PHI to wrong recipients, leaving computers unlocked, or accessing records they shouldn’t see.
Here are some resources and insights to know in detail about HIPAA laws:
HIPAA sets minimum standards, not best practices. Organizations that excel at data protection go further than regulations require. Strong privacy programs create competitive advantages.
Patients choose providers they trust with sensitive information. Data breaches damage reputations for years and drive patients to competitors.
The healthcare industry faces more cyberattacks than any other sector. Ransomware groups target hospitals because they’ll pay quickly to restore operations. But organizations with robust security programs recover faster and maintain patient confidence.
HIPAA compliance isn’t a one-time project. It’s an ongoing commitment to protecting patient privacy while delivering quality care.
Get it right, else there can be dire consequences. Contact us now to know how our experts can help.